Authentication
Siren Alert supports authentication using Search Guard Classic. There are several options available.
Authenticate search request
Kibana https://www.elastic.co/guide/en/elasticsearch/client/javascript-api/current/auth-reference.html[Elasticsearch basic authentication] is used for authentication.
Valid certificate
sentinl:
settings:
authentication:
enabled: true
username: 'elastic'
password: 'password'
cert:
selfsigned: false
pem: '/path/to/pem/key'
Self-signed certificate
sentinl:
settings:
authentication:
enabled: true
username: 'elastic'
password: 'password'
cert:
selfsigned: true
Siren Platform
Authenticate Siren Alert using single user - default sentinl from
Access Control app. For example, default investigate.yml.
+
# Access Control configuration investigate_access_control: enabled: true cookie: password: "12345678123456781234567812345678" admin_role: kibiadmin sentinl: elasticsearch: username: sentinl password: password ...
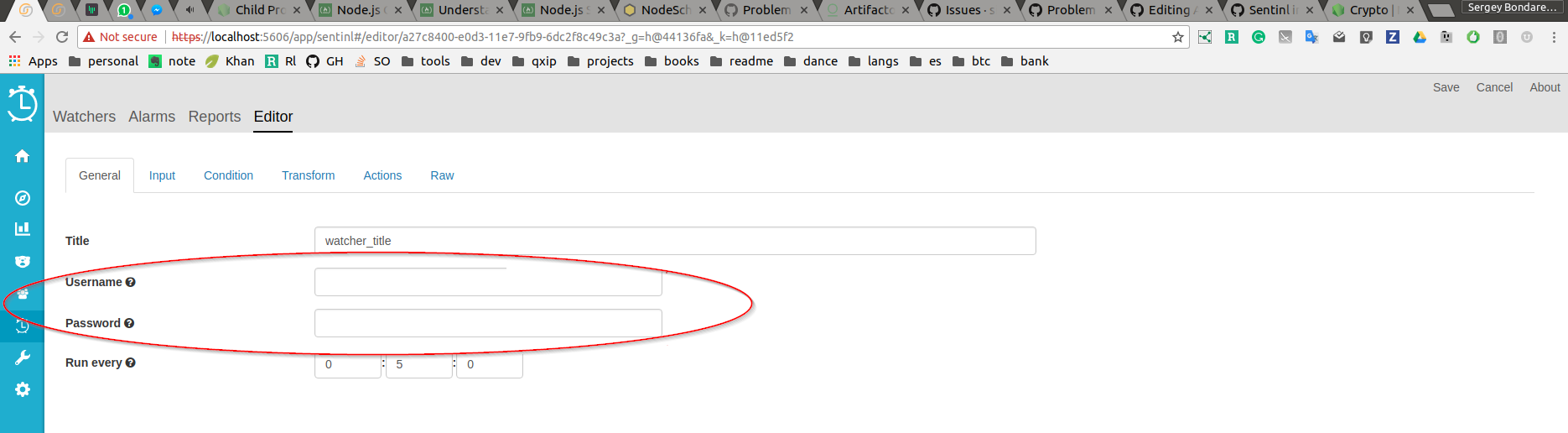
Siren Platform or Kibana
It is possible to create multiple user credentials and assign these credentials to watchers, one credential per watcher, thereby authenticating each watcher separately. It is called impersonation.
-
Create credentials in Search Guard Classic or X-Pack and assign the permissions you need. You need one user for Sentinl and one user per watcher.
-
Set Siren Alert authentication.
sentinl: settings: authentication: enabled: true impersonate: true username: 'elastic' password: 'password' sha: '6859a748bc07b49ae761f5734db66848' cert: selfsigned: true-
Set password as clear text in
passwordproperty. The password can be put in encrypted form instead. Set password hash inshaproperty, now you can removepasswordoption. -
Use
sentinl/scripts/encryptPassword.jsscript to obtain the hash. Edit the value of theplainTextPasswordvariable, replacingadminwith your password. Copy the generated hash and paste as theshavalue. Also, you can change password hashing complexity by setting options insideencryption. Node.js crypto library is used to hash and unhash user password.
-
-
Set watcher authentication.
encryptPassword.jsimpersonate: true`.passwordusername`